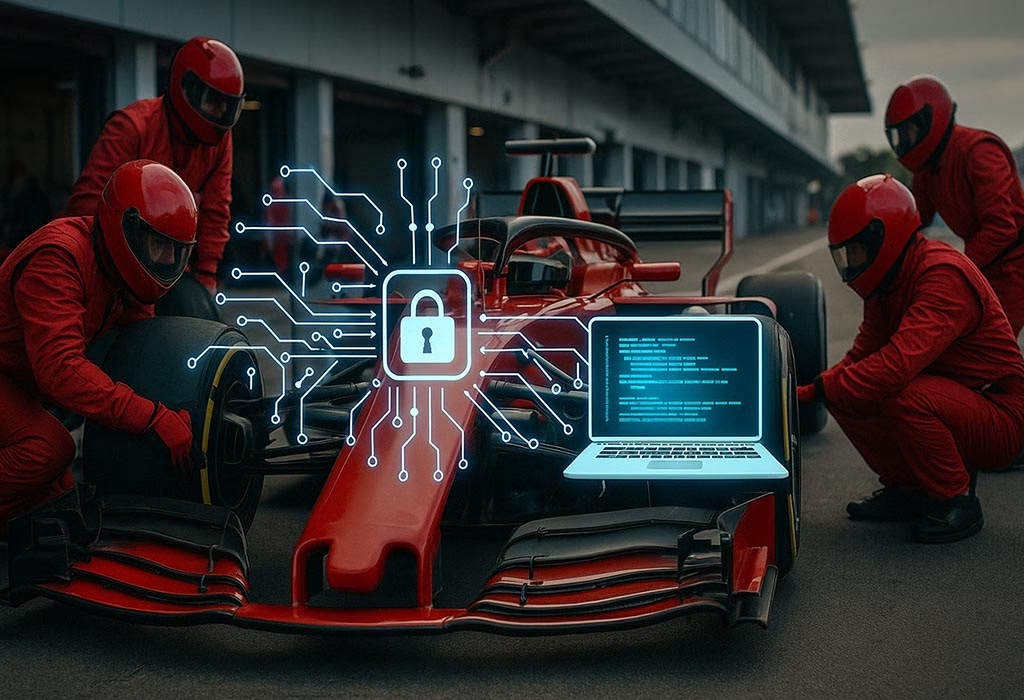
Formula 1 is not just the world’s fastest motorsport — it is one of the most data-intensive industries on the planet. Each race weekend generates terabytes of telemetry, engineering intelligence, and logistical data that teams depend on for split-second decisions worth millions of dollars. That makes F1 an increasingly attractive target for cybercriminals, nation-state actors, and corporate spies. In this article, we examine the real cybersecurity threats facing Formula 1 teams, explore documented real-world attack scenarios, and break down how teams are actively defending their competitive edge in 2026.
Why Formula 1 Is a Prime Cybersecurity Target
F1 teams operate at the intersection of high-performance engineering, real-time data analytics, and global logistics — making them one of the most attractive targets for cyberattacks in professional sports. Several interconnected factors explain why:
- Extreme data dependency: Race strategy, car setup, and performance optimization rely entirely on real-time telemetry. Compromising that data stream could cost a team the race — or the entire championship.
- Distributed infrastructure: Factories in Europe, trackside systems at 24 international venues, cloud platforms, and remotely connected engineers all share the same network ecosystem.
- Valuable intellectual property: Aerodynamic simulations, CFD models, and proprietary algorithms represent hundreds of millions in R&D investment — and a goldmine for competitors.
- Broad attack surface: Third-party vendors, software providers, and hardware suppliers each introduce new vulnerabilities into the chain.
- Geopolitical exposure: Racing in countries with active state-sponsored cyber programs significantly increases the risk of targeted surveillance and espionage.
Because of this complexity, cybersecurity in Formula 1 goes far beyond standard IT protection — it has become a core component of competitive advantage.
Protection of Sensitive Telemetric Data
Modern F1 cars carry over 300 sensors generating up to 3GB of data per race. This telemetry is transmitted in real time between the car and multiple engineering stations — both trackside and at the remote “Mission Control” centers that major teams operate from their factories.
- Data interception risk: Wireless telemetry streams are a potential target for interception. If a competitor gained access to live setup data or tyre degradation models, the strategic consequences could be decisive.
- Data manipulation: A more sophisticated scenario involves not just reading the data, but subtly corrupting it — feeding false sensor readings to engineers making live strategy calls during a race.
- Pipeline security: Teams use encrypted communication channels and dedicated private networks for data transmission, but managing this consistently across 24 global venues creates persistent vulnerabilities throughout the season.
Communication Security
The radio communications between drivers and race engineers are one of Formula 1’s most recognizable elements — and one of its most exposed attack surfaces.
- Radio interception: Race team frequencies have historically been straightforward to scan. While modern F1 uses encrypted digital radio systems, the risk of unauthorized monitoring during a race weekend — particularly at circuits in high-risk regions — remains real.
- Pit wall systems: The laptops, analysis tools, and real-time strategy software deployed on the pit wall are high-value targets. A denial-of-service attack timed to a safety car window could force a strategically catastrophic decision with no time to recover.
Cyberattacks and Industrial Espionage
Formula 1 generates billions of dollars in value, and championships can be decided by thousandths of a second. This makes the sport a natural target for industrial espionage — both digital and human.
- Phishing and social engineering: Engineering staff are high-value targets. A well-crafted spear-phishing email targeting a performance engineer could yield access to months of simulation data with a single click.
- Supply chain attacks: A compromised supplier — whether software, hardware, or data analytics — can serve as a backdoor into a team’s infrastructure without ever directly attacking it.
- Ransomware: A ransomware attack launched before a race weekend — targeting factory simulation systems or logistics platforms — could cause catastrophic disruption at the worst possible moment.
Security Challenges in Global Events
With 24 races across five continents, F1 teams must continuously adapt their security posture to widely varying risk environments.
- Network exposure at international venues: Using local networks at circuits — including some in countries with documented state-sponsored hacking programs — introduces risks that teams operating in familiar home environments rarely face.
- Fan and sponsor data: Millions of fans interact digitally with F1 brands, and sponsors share sensitive contractual and financial data with teams. This commercial data layer is an increasingly attractive target for financially motivated threat actors.
Real-World Cybersecurity Incidents in Formula 1
Cybersecurity is not just a theoretical concern in Formula 1 — documented incidents reveal that the threat is both real and escalating.
The Renault F1 Team Espionage Scandal (2007)
In one of the most damaging cases in F1 history, Renault was found in possession of over 780 pages of confidential McLaren technical documentation, including detailed specifications of key car components. While not a traditional hack, this case established how devastating the theft of digital intellectual property can be — and prompted the FIA to significantly strengthen data security rules across the sport.
Williams Racing’s Augmented Reality App Leak (2021)
Ahead of the launch of a new AR app for their 2021 car reveal, Williams Racing suffered a data breach that exposed confidential car images and app features before the official announcement. The incident highlighted vulnerabilities in digital asset management and third-party app development pipelines — risks that apply to every team managing digital fan experiences at scale.
Lessons from These Breaches
A common thread runs through F1’s most serious cybersecurity incidents: the most damaging breaches rarely involve sophisticated zero-day exploits. They typically exploit human error, third-party vulnerabilities, or inadequate access controls. For F1 teams — and any data-driven organization — the weakest link is rarely the firewall. It is the human being behind it.
How Formula 1 Teams Defend Against Cyber Threats
Leading F1 teams have invested heavily in cybersecurity infrastructure in recent years. Here is how the best teams approach digital defense:
- Security Operations Centers (SOC): Major teams now operate dedicated SOCs — sometimes 24/7 during race weekends — staffed by security professionals who monitor for threats in real time.
- Zero Trust Architecture: Assuming no user or device is inherently trusted, teams implement strict identity verification and least-privilege access across their entire network, both at the factory and trackside.
- Red team exercises: Teams regularly simulate cyberattacks — including mock data theft and ransomware scenarios — to stress-test defenses before real incidents occur.
- Supply chain vetting: With supply chain attacks well understood, top teams apply rigorous cybersecurity requirements to all technology vendors and component suppliers.
- Staff security training: Since phishing and social engineering remain the most common attack vectors, regular awareness training for engineers, strategists, and management staff is now standard practice at competitive teams.
- FIA cybersecurity regulations: The FIA has progressively strengthened cybersecurity requirements within its Sporting and Technical Regulations, mandating minimum standards for data protection and incident reporting across all teams.
Conclusion
The cybersecurity challenges in Formula 1 mirror a broader truth about the digital age: wherever there is competitive advantage, there is a target. In a sport where milliseconds separate champions from also-rans, protecting data and communications infrastructure is as critical as optimizing downforce or tyre strategy. As F1 continues to evolve — with more connected cars, more remote engineering, and more digital fan engagement — the cyber threat landscape will only grow more complex. For teams that want to win, cybersecurity is no longer optional. It is part of the race.
At MicroHackers, we help organizations understand and address exactly these kinds of evolving threats. Contact us or use our Criticality Profile Calculator to identify which of your systems would be most targeted.